At Brightmind, we don’t just invest in companies—we back visionary founders solving critical problems in cybersecurity. When we met the SGNL team, it was clear they weren’t just another security startup; they were rethinking privileged identity management (PIM) from the ground up. Here’s why we knew SGNL was a game-changer.
A Team Built for This Mission
SGNL’s founding team isn’t new to identity security. SGNL is led by identity legends (as well as great human beings) Scott Kriz, Erik Gustavson and Atul Tulshibagwale who bring half a century of experience driving innovation in the space. Having previously built and sold companies to Google, as well as pioneering the invention of CAEP, they know exactly what it takes to redefine an industry. Their expertise, combined with deep technical acumen, gives us confidence that they can build a category-defining solution.
A Greenfield Approach to a Legacy Problem
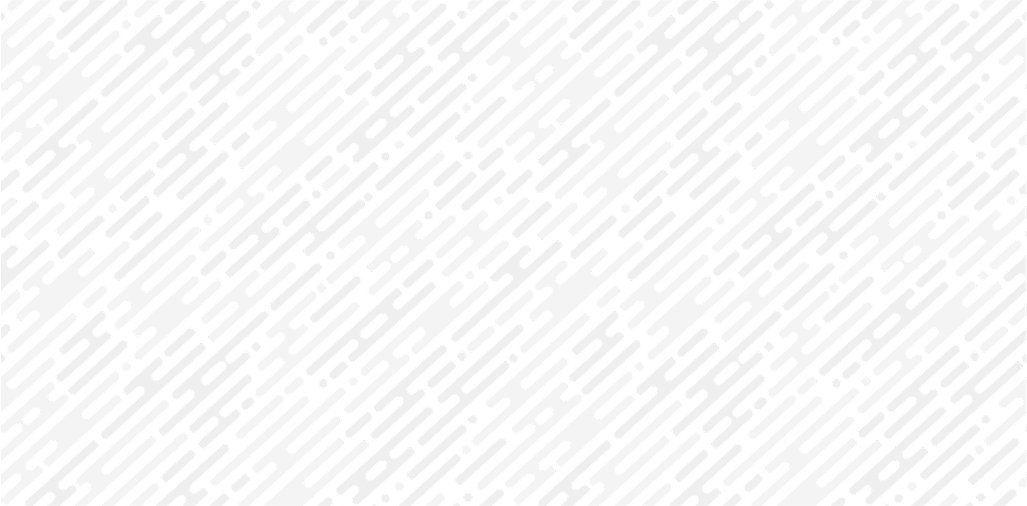
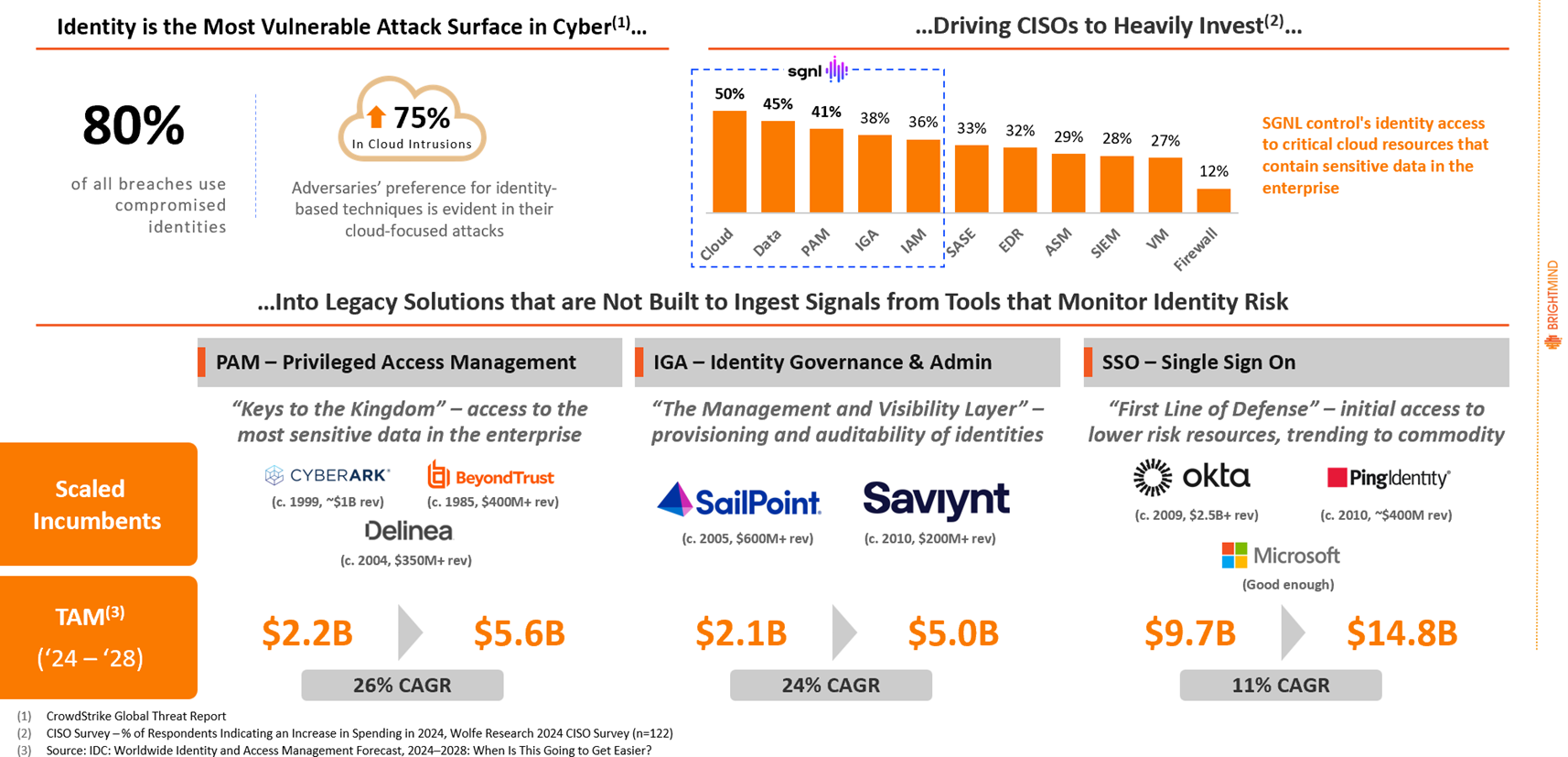
When we started Brightmind, we focused heavily on evaluating the adversary landscape, operator pain-points and components of the security stack that are not living up to their potential. Most privileged access solutions today operate on static, pre-configured permissions—leaving enterprises exposed to insider threats and credential abuse. SGNL’s real-time, context-aware approach eliminates standing privileges, ensuring users only have access when they actually need it. This isn’t just an incremental improvement—it’s a fundamental shift in how identity security should work. While identity-based attacks are the most prominent entry points into modern enterprise networks, the incumbent vendors lack the architecture to evaluate risk and enforce contextual access. Adversarial activity, not efficacy, is driving enormous spend to the incumbents.
A Market Hungry for Change
With the rise of AI-driven security threats and stricter compliance regulations, enterprises are looking for more adaptive, zero-trust access models. SGNL’s approach aligns perfectly with this demand, making it well-positioned for adoption among Fortune 500 and high-growth companies alike.
Identity solutions should be a force multiplier in the enterprise security stack. Dynamic access is, in many ways, the most elegant response to contain a threat, but two key pieces of technology are needed: 1) shared signals or integrated ingestion of risk from tools within the enterprise environment and 2) policy-driven, flexible access control to enforce based on those shared signals. SGNL is a central nervous system for identity security, integrating with the core identity capabilities in the enterprise environment (SSO for authentication, privilege portals for crown jewel access, etc.) to shift them from the static tools they are today to the dynamic enforcement tools operators need to respond to risk at adversary speed.
Early Traction with the Right Buyers
We have seen a significant trend in “identity transformation” projects among large enterprises. They simply feel it’s time to replace 20-year-old legacy identity technologies. In many ways we view this as recognition that the gap between spend and efficacy is too significant in identity using incumbent approaches. SGNL has the opportunity to become a key piece of what constitutes identity transformation – enabling enterprises to dynamically enforce access based on risk, balance user friction while reducing standing privilege and, importantly, get more out of their security and infrastructure investments.
Despite launching their product only recently, SGNL has already gained attention from leading security teams. Their focus on F500 adoption and repeatable go-to-market execution set them apart from early-stage competitors.
Our Conviction in SGNL’s Future
We believe SGNL has the potential to become the gold standard for privileged identity management. The combination of strong leadership, a bold vision, and a massive market opportunity made our decision to invest an easy one.
We couldn’t be more excited to support SGNL on their journey—and if you’re in security or identity access management, you should be paying close attention.
Stay tuned.
Let's Secure Tomorrow, Together.
We're always looking for the next generation of cybersecurity innovators. Reach out to our team to start the conversation.
Other Articles
Artemis: Reimagining Security Operations for the AI-Era
Brightmind Partners announces their investment in Artemis, a new security operations platform founded by Shachar Hirshberg and Dan Shiebler (former leaders at AWS and Abnormal Security) that aims to reimagine SIEM for the AI era. The company introduces "adaptive protection," an approach that automates detection, investigation, and response by embedding deep enterprise context into an autonomous detection lifecycle, eliminating false positives and evaluating threats as complete attack stories. Unlike traditional SIEMs built on centralized data ingest and retention economics, Artemis offers architectural flexibility that works across multiple SIEMs, datastores, or its own storage, avoiding vendor lock-in. Brightmind praises the team's rapid execution—building in six months what the SIEM space has attempted for over a decade—along with their strong customer-obsessed culture.
What everyone seems to be overlooking with Mythos and Project Glasswing
Stephen argues that while Mythos (an AI security model) giving 50 companies a 90-day head start to find vulnerabilities sounds promising, it's largely illusory — enterprises are already drowning in unpatched critical vulnerabilities and the remediation pipeline is far too slow and contentious to meaningfully close the gap in time. On day 91, when Mythos is broadly released, whatever defensive advantage was gained evaporates and attackers gain the same powerful exploit-generation capability. He recommends CISOs restructure their security orgs entirely — retiring traditional scanning teams in favor of one massive remediation-focused team, letting AI handle identification while humans focus solely on fixing. His deeper fear is that these capabilities will trickle into small, offline, guardrail-free local models, democratizing exploit generation in a way that creates systemic risk far beyond what any centralized tool with access controls can contain.