At Brightmind Partners we look for founders with lived experiences that drive them to take on large, complex problems. Onit Security founder, Ofer Amitai , experienced the significant consequences of an unmanageable vulnerability backlog that resulted in the compromise of his prior company, Portnox. With the weight of that experience, the Onit team aggressively pursued a new approach to exposure management, utilizing AI to unify true business context with risk signals across the enterprise and close the gap at unprecedented speed and scale.
A Challenge Built for the AI-era
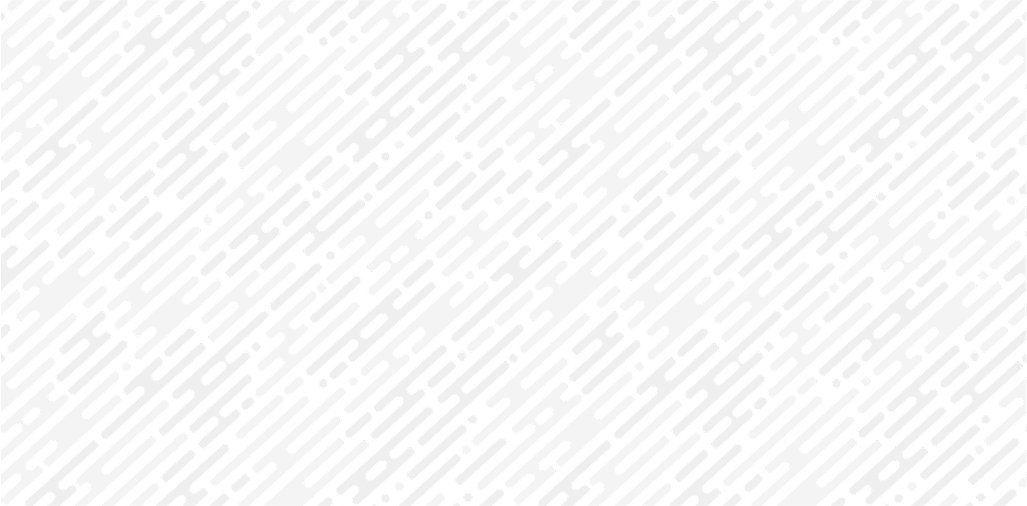
Traditional vulnerability and exposure management has been focused on silos, utilizing scanners to identify risk within domains. In talking with operators, we saw a significant trend towards homegrown solutions to tackle the unification challenge. Despite the presence of tools in RBVM and UVM over the past half decade, we found considerable levels of supplementation to engineer a business process compatible with the needs of the enterprises. With enormous tool sprawl and increasing IT complexity. No two customer environments truly look the same. Efforts to manage the holistic vulnerability pipeline historically have been nearly impossible due to three primary factors 1) limited business context regarding the underlying assets 2) the ability to define prioritization consistently 3) the ability to take action seamlessly without generating unintended consequences.
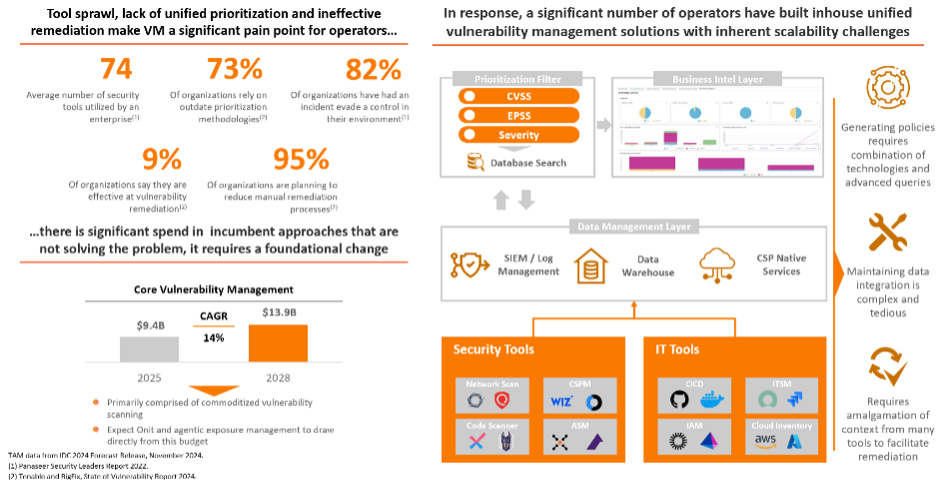
AI has fundamentally shifted this paradigm, enabling business context and reasoning to drive each decision in the vulnerability management lifecycle at machine speed.
The Onit platform enables customers to embed their feedback into the engine, ensuring that the actions that are driven by the platform align to their unique concept of risk. This is a decision-based architecture, an AI-native approach that allows operators to autonomously respond to threats as they emerge, closing the gaps as they open. With adversaries driving breakout times in as little as 27 seconds using AI, it is critical that we build the foundation for autonomous vulnerability management today.
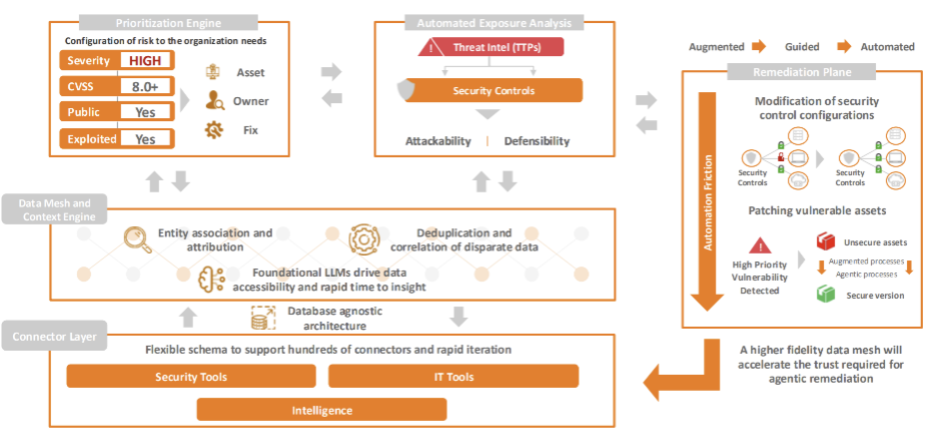
Beyond the risk profile, there are also significant productivity gains to be realized by automation in this domain, and we expect that forward-looking operators will heavily value the time and focus their IT and engineering teams recover as a result.
We could not be happier to partner with Elad Ben Meir , Ofer Amitai , Tom Winter and the Onit Security team! Their relentless desire to reshape this market motivated us from day one to be a part of their journey.
Let's Secure Tomorrow, Together.
We're always looking for the next generation of cybersecurity innovators. Reach out to our team to start the conversation.
Other Articles
Artemis: Reimagining Security Operations for the AI-Era
Brightmind Partners announces their investment in Artemis, a new security operations platform founded by Shachar Hirshberg and Dan Shiebler (former leaders at AWS and Abnormal Security) that aims to reimagine SIEM for the AI era. The company introduces "adaptive protection," an approach that automates detection, investigation, and response by embedding deep enterprise context into an autonomous detection lifecycle, eliminating false positives and evaluating threats as complete attack stories. Unlike traditional SIEMs built on centralized data ingest and retention economics, Artemis offers architectural flexibility that works across multiple SIEMs, datastores, or its own storage, avoiding vendor lock-in. Brightmind praises the team's rapid execution—building in six months what the SIEM space has attempted for over a decade—along with their strong customer-obsessed culture.
What everyone seems to be overlooking with Mythos and Project Glasswing
Stephen argues that while Mythos (an AI security model) giving 50 companies a 90-day head start to find vulnerabilities sounds promising, it's largely illusory — enterprises are already drowning in unpatched critical vulnerabilities and the remediation pipeline is far too slow and contentious to meaningfully close the gap in time. On day 91, when Mythos is broadly released, whatever defensive advantage was gained evaporates and attackers gain the same powerful exploit-generation capability. He recommends CISOs restructure their security orgs entirely — retiring traditional scanning teams in favor of one massive remediation-focused team, letting AI handle identification while humans focus solely on fixing. His deeper fear is that these capabilities will trickle into small, offline, guardrail-free local models, democratizing exploit generation in a way that creates systemic risk far beyond what any centralized tool with access controls can contain.