A Continuous Identity Approach: Stopping the Threats of Tomorrow, Today
The level of activity in identity over the course of the last twelve months has been nothing less than transformative, but not all strategies are created equal. While identity is a pillar of enterprise security strategies, there has historically been a considerable disconnect between SecOps and access management. SGNL was built from the ground up to address this gap, to connect critical data into the context of access decisions in real time, unlocking the full potential of identity to drive security outcomes. Whether at the point of an access request or in the midst of a session, SGNL continuously adapts and eliminates risks as it emerges.
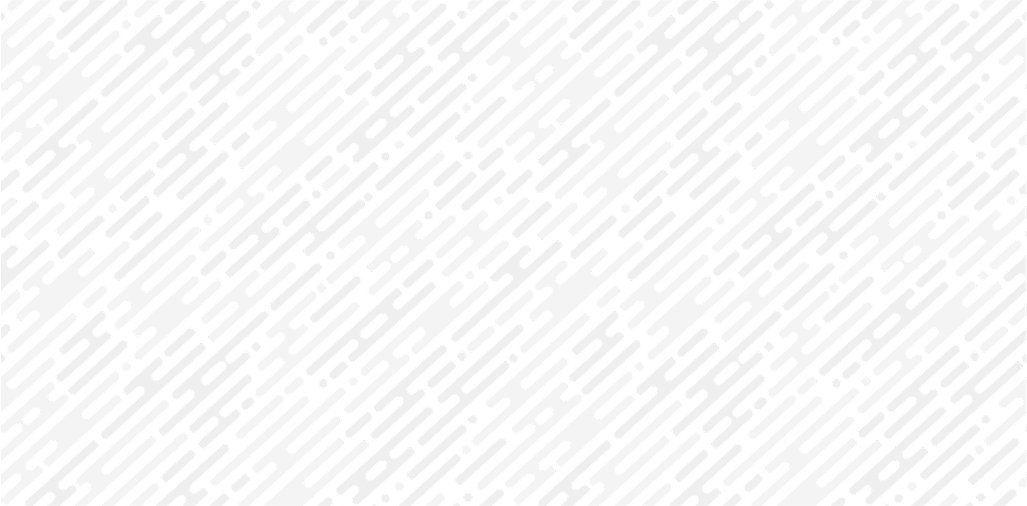
Example of SGNL enabling dynamic access to critical cloud infrastructure.
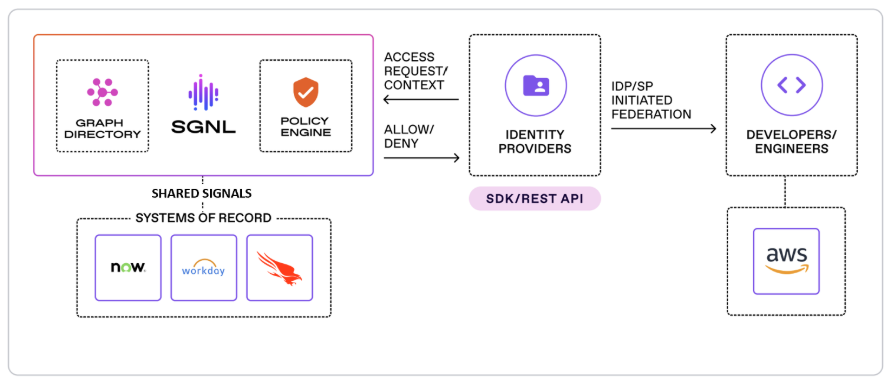
The rapid adoption of AI is pushing the traditional static approaches utilized by PAM vendors to their breaking point. Enterprises need to contextualize access decisions at unprecedented speed to safely unlock the productivity gains of AI agents. With their dynamic architecture, SGNL enables organizations to deploy and manage agents without compromising their zero trust standards.
Example of SGNL managing access policies to sensitive data between MCP clients and servers.
An Identity Security Platform Emerges
CrowdStrike stops breaches, an always on, continuous mission. An analytics powerhouse, CrowdStrike processes more than a trillion events a day with sub second latency – their platform has never been static. CrowdStrike’s first act in identity began with threat detection, deploying sensors to domain controllers to help detect and respond to threats against active directory. The second act came in the form of cloud-based identity visibility, posture, and detections. Between the two, CrowdStrike is the most complete identity threat detection offering on the planet by a strong margin. However, identity threat detection is a small component of the overall identity stack, albeit a highly differentiated offering that identity native vendors have struggled with, and without a differentiated offering in access management CrowdStrike’s reach was limited.
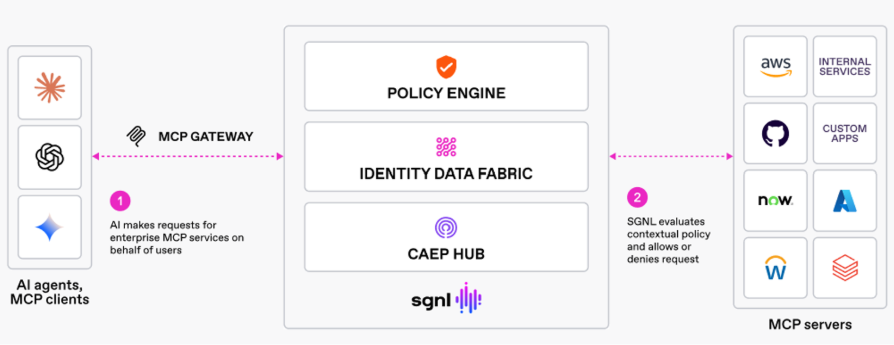
The integration of SGNL enables CrowdStrike to merge detection and access management within a consolidated platform delivering threat driven, continuous identity. This new paradigm embeds security analytics into the identity stack to enable zero trust purpose built for the agentic era.
Threat driven continuous identity enables dynamic access and enforcement over critical data
Congratulations to Scott Kriz , Erik Gustavson and the SGNL team – you are truly a team built for this mission. Brightmind is extremely proud to have been a part of your journey. Together with CrowdStrike, we know you will transform identity security.
Link to the press release: https://ir.crowdstrike.com/news-releases/news-release-details/crowdstrike-acquire-sgnl-transform-identity-security-ai-era
Let's Secure Tomorrow, Together.
We're always looking for the next generation of cybersecurity innovators. Reach out to our team to start the conversation.
Other Articles
Artemis: Reimagining Security Operations for the AI-Era
Brightmind Partners announces their investment in Artemis, a new security operations platform founded by Shachar Hirshberg and Dan Shiebler (former leaders at AWS and Abnormal Security) that aims to reimagine SIEM for the AI era. The company introduces "adaptive protection," an approach that automates detection, investigation, and response by embedding deep enterprise context into an autonomous detection lifecycle, eliminating false positives and evaluating threats as complete attack stories. Unlike traditional SIEMs built on centralized data ingest and retention economics, Artemis offers architectural flexibility that works across multiple SIEMs, datastores, or its own storage, avoiding vendor lock-in. Brightmind praises the team's rapid execution—building in six months what the SIEM space has attempted for over a decade—along with their strong customer-obsessed culture.
What everyone seems to be overlooking with Mythos and Project Glasswing
Stephen argues that while Mythos (an AI security model) giving 50 companies a 90-day head start to find vulnerabilities sounds promising, it's largely illusory — enterprises are already drowning in unpatched critical vulnerabilities and the remediation pipeline is far too slow and contentious to meaningfully close the gap in time. On day 91, when Mythos is broadly released, whatever defensive advantage was gained evaporates and attackers gain the same powerful exploit-generation capability. He recommends CISOs restructure their security orgs entirely — retiring traditional scanning teams in favor of one massive remediation-focused team, letting AI handle identification while humans focus solely on fixing. His deeper fear is that these capabilities will trickle into small, offline, guardrail-free local models, democratizing exploit generation in a way that creates systemic risk far beyond what any centralized tool with access controls can contain.